On Computer Security in the Mobile Age
I was looking over a stack of old conference papers and found this review of the paper written by myself in collaboration with Lucijan Carić, which we presented in 1996 at the Virus Bulletin Conference in Brighton, UK.
"After a welcome coffee break, Joe Wells (IBM) presented a paper on the PC-virus ‘hot zones’, after which Lucijan Caric and Boris Debic provided a timely reminder of the implications of an Internet-enabled world: if malware is able to send data silently to remote sites, then the problems, unfortunately, are all too clear."
The presentation was immediately following Joe Wells'. This was quite a recognition at the time, as Joe is and was back then widely regarded as one of the foremost experts in understanding security threats in the wild.
The paper had a couple of highlights. It was the first to establish a new class of threats. A category where threats would take advantage of the Internet, not only as a propagation medium as was already shown by Morris' out of control experiment with the Internet Worm, but a category where the threat uses the Internet for propagation, command and control, and data exfiltration or corruption. Keep in mind that at the time of this conference most computer viruses used media such as floppy disks, or removable hard disks for their propagation. The Internet was still in its early commercial days, not many nodes were yet connected at the approximately 10,000 institutions connecting to it. The protocols in use were fairly simple and without many features which could be exploited. After all they were designed for a benign and mostly collaborative academic setting.
"Morris thought he would need to build a 'global database' of infected computers. However, he admitted, doing that could prove 'really hard.' By the time he released the worm two weeks later, he had only made small steps toward implementing these ideas. He never created a command-and-control system that would have allowed him to send instructions to infected machines."
The key part of the paper was a full description followed by a demo of an example exploit which used a command and control intermediary to take complete control of the target computer system. The publication of this threat received a great deal of attention by researchers from industry, notably IBM and MacAffee whose representatives took part at the conference. It was not until almost three years later when the first attack using this combination was reported. Two trends were of particular consequence for creating a fertile field for these type of attacks. The first was the growing peopularity of the Internet browser and consequently a rise in the number of computers serving http and other protocols.
"In 1996, Netscape's share of the browser market reached 86% (with Internet Explorer edging up 10%); but then Microsoft began integrating its browser with its operating system and bundling deals with OEMs, and within two years the balance had reversed."
The number of computers and PCs connected to the Internet started a phase of rapid growth. Second - legislature was going through the U.S. Congress and Senate to place incentives for turning the Internet from an academic infrastructure to a commerce medium benefiting wider society.
"Four major versions of the Internet Tax Freedom Act currently are under consideration. The Senate version of this proposed legislation, S. 442, was approved in amended form by the Commerce, Science, and Transportation Committee on November 4, 1997. The House version, H.R. 1054, was approved in amended form by subcommittees of both the Commerce and Judiciary Committees on October 9, 1997. A new Senate version (S. 1888) called the "Internet Fairness and Interstate Responsibility Act"
July 8, 1997 was my first summer in Silicon Valley. I clearly remember when Internet traffic records were broken as NASA's website started serving images taken by Pathfinder on Mars. Many of these I have downloaded myself and they are still burned on CDs in my archive. Remember this was a time before Google and the ubiquity of information and it being available at any time provided a connection. This internet based broadcast generated 46 million hits in just a single day. The Internet reached a critical mass where it was now an important part of the way we consume and publish news (the word blog or web log was coined the same year), the way we communicate, and in the way we start to transact business. It is the following year, in 1998, when the the threat model described by us at the VB 1996 conference was reported. CNN reported:
"They created and released the program Back Orifice last year to the general public at the Las Vegas hacker and security conference DEF CON. The program allows its users to remotely control victims' desktops, potentially undetected. At this year's conference, on July 9, Sir Dystic says the cult will outdo itself and release Back Orifice 2000. The program, he says, is smaller, nimbler, and twice as nefarious."
Security experts had a mixed feeling about making a security point by releasing the threat into the open. But they also warned against Microsoft's lack of priority when it comes to how they treat the security of their operating system. Something which will be a thorn in Microsoft's side for many years to come.
"Computer security experts question the Cult of the Dead Cow's intent. Releasing a hacking tool like Back Orifice 2000 in the name of safeguarding computer privacy is a bit like the American Medical Association infecting cattle with the deadly e. coli bacteria to inspire food companies to sell healthier meats."
Back Orifice and its successor Back Orifice 2k (shortened to BO and BO2k) are a computer program designed for remote system control. It enabled a user to control a computer running the Microsoft Windows operating systems of the time from a remote location. This included control of the input devices, surveillance of the target computer, firewall tunneling, hiding its presence from the unsuspecting user and other capabilities. The name was a play on words of Microsoft BackOffice Server software.
It is exactly this scenario that we have predicted in our 1996 paper. From then on the phenomenon of Internet channel enabled threats, as we dubbed them then, only continued to grow and expand in reach. Currently such threats poise serious challenges not only for users and companies but to entire economies and states. Many non-state and state actors continue developing their capabilites in this area to enagage in both defensive and offensive activities.
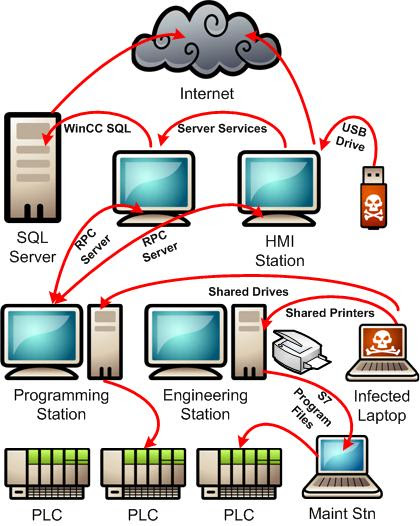
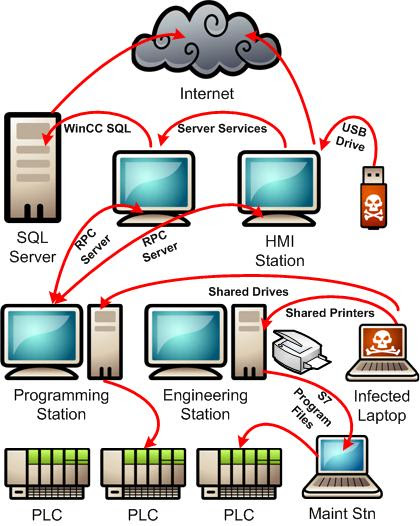
I should point the reader to Stuxnet, probably one of the best documented examples of this family of software from the desktop era developed jointly by the US and Israel. While we in our paper from the perspective of computer security experts described the system as a threat, it's needless to say that any such system can and will likely be used as a cyberweapon, where a cyberweapon is defined as a malware agent employed for military, paramilitary, or intelligence objectives.
What is the future?
With the increased pervasiveness of mobile computing. The expanding ways in which mobile devices can excahnge data. To mention a few; over cell connections, over internet connections, through low energy proximal connectivity i.e. blue tooth but also sound waves or LED signaling. In addition, mobile devices travel around with us and collect data all day long. It can be data about ourselves (privacy) or data about the places we work at or visit (physical security) or the places at which we gather (event security and intelligence).
It should be fairly obvious that the complexity of defense against this new expanded category of capabilities will be very hard without an approach that takes a different look at computer and software security in the future.
With this new wave of growth of complexity and interconnectedness I am reminded of a thought by Gene Spafford (pic. above) who visited us a few weeks back. Without considering the whole picture and threat risk it is impossible to defend effectively from a threat in a complex system with many communication pathways.
"Secure web servers are the equivalent of heavy armored cars. The problem is, they are being used to transfer rolls of coins and checks written in crayon by people on park benches to merchants doing business in cardboard boxes from beneath highway bridges. Further, the roads are subject to random detours, anyone with a screwdriver can control the traffic lights, and there are no police."
Unfortunately in today's world we are still unable to completelly secure our servers, the economic damages keep growing and new ones are popping up in competitiveness and intelligence. Myself I am still on an identity theft alert program instituted at great cost by the company through which I had my health insurance plan. I still receive the post-theft status reports each month, as a grim reminder of the security reality. I am also reminded of my good friend a long time government and NASA employee who went to great strides to avoid using social networks to avoid her personal and social network data would not end in the wrong hands. We had a chat about a month ago and she reminded me of her efforts and how frustrating it was to leanr about this bit of news:
"The Office of Personnel Management (OPM) said data stolen from its computer networks included Social Security numbers and other sensitive information on 21.5 million people who have undergone background checks for security clearances."
The Mobile World
We are doing a better job in many respects than decades ago, but there is still more to be done, and more paradigms to be shifted or broken. The mobile computing ecosystem is only adding to the already complex reality and it will be imperative in the coming years to understand fully its consequences on the security landscape. And while leaders are thinking in new more adaptable ways about computer security today. It is still true, as it was back in 1996, that a new paradigm brings its own new qualities which have to be understood in order to properly build defenses - and it seems inevitable - offenses for its age. The major qualities brought by mobility in computing have already been mentioned but few which are novel and not seen in prior times are;
- the ability to take massive ammounts of data and computing power nibly across locations and geographies,
- and the ability to pop in and out of established or ad-hoc networks and meshes at any time.
These are probably the most interesting aspects of ubiquitous mobile computing that need to be researched from a security perspective, and they are being researched from other economic perspectives already. There are also significant differences in how different mobile leaders implement security paradigms on their platforms depending on whether they have the advantage of full control of their hardware and software platform or they are building a platofrm relying on open source and not targeting specific hardware. Both approaches have their strengths and weaknesses.
Hopefully the time gap between mobile's economic significance and proper security will be less delayed than in the previous paradigm shift - when the Internet changed profoundly computer security in the late 90's.
Boris Debic.
12/5/2015.
San Mateo, CA.



Comments